How to Make a Raspberry Pi VPN Server
The Raspberry Pi has a ton of different uses. Since it's small and energy-efficient, uses such as a network-attached storage (NAS) device, media server, game server, smart home hub, or any number of Internet of Things (IoT) projects run extremely well on the Raspberry Pi. Since the credit-card-sized Raspberry Pi sports a tiny footprint and sips power, it's ideal for an always-on device. And with superb internet connectivity, whether running on a wireless network or via a wired Ethernet port, the Pi is suitable for handling network traffic. Learn how to build a Raspberry Pi VPN (virtual private network) server!
What is a VPN and Why Should You Use One?
Ok, so what is a VPN? It's a virtual private network, a means of connecting to the internet with a secure, private connection. Rather than using your IP address, network traffic is routed through a gateway server, so you'll have public-facing IP address of another location. For instance, you might be located in New York City, but with your VPN, making it look as if you're connecting in London, UK.
Great, but why should you use a VPN? There are tons of motivations for using a VPN. With an increasing number of snooping ISPs (internet service providers), many users simply want the security of a VPN masking their web traffic. Since you can use VPN servers for different countries, a VPN offers a nifty means of unlocking geo-protected content. Perhaps you're based out of the UK, but traveling to the United States, and still want to be able to stream the BBC. A VPN can help with that. On public, unprotected Wi-Fi, a VPN adds a layer of security by masking your IP address. Plus, many VPN options alow you to set up a home VPN server for connecting to your home network from anywhere, a useful feature for the likes of server management. (Note: we at Electromaker do not condone illicit activity, so please only use a VPN for legal actions).
Why use a VPN:
- Mask your IP address
- Hide from snooping ISPs
- Extra security on public Wi-Fi
- Unblock geo-restricted content
- Connect to your home network from anywhere
How to Build a Raspberry Pi Raspberry Pi VPN Server
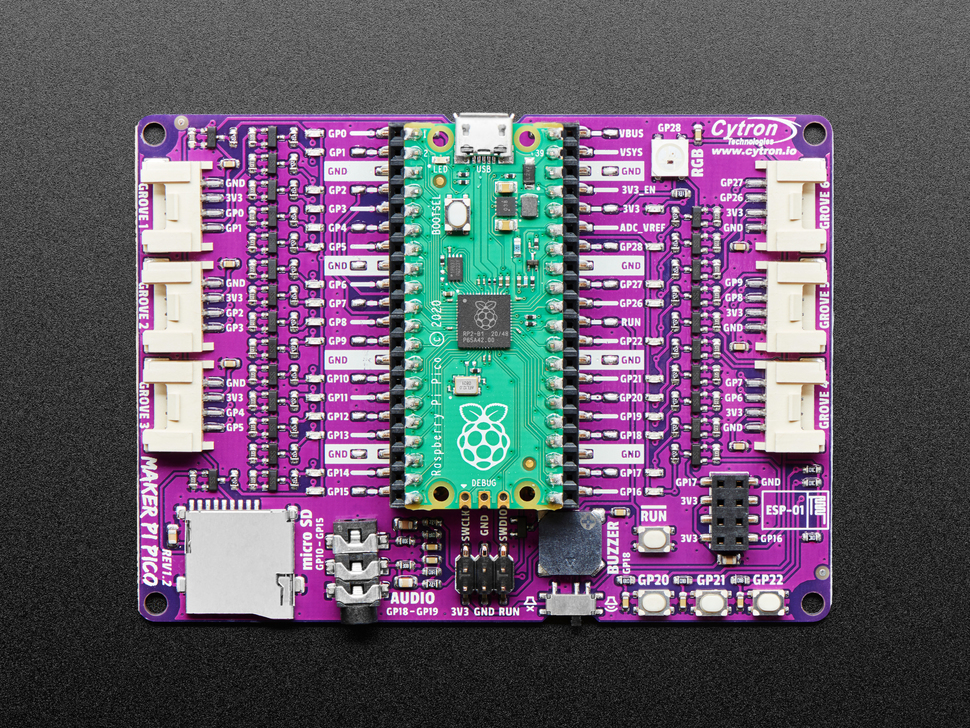
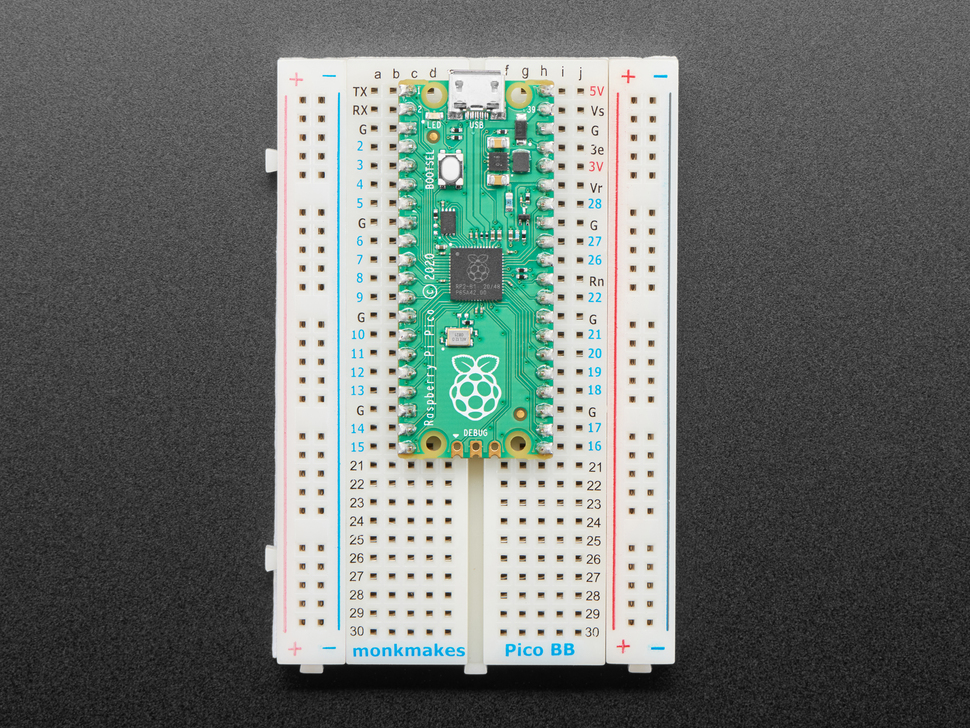
A Raspberry Pi VPN server is pretty easy and cheap to build. You'll need a Raspberry Pi board, compatible Linux operating system such as the Debian-based Raspbian, a VPN provider, power supply, microSD card for hosting your operating system (OS), and optional but recommended case. You'll also require an active internet connection, peripherals including a keyboard and mouse, plus a display of some kind. While you can use your Raspberry Pi hooked up to a display such as a monitor, TV, or projector, you might prefer to SSH into your Raspberry Pi instead.
What you'll need for a Raspberry Pi VPN server:
- Raspberry Pi board (Raspberry Pi 4 recommended)
- Debian-based Linux distribution (distro) such as Raspbian
- VPN software i.e. OpenVPN or Wireguard
- Case
- microSD card
- Keyboard/mouse and/or host PC
- Monitor/TV/projector for a display
- Active internet connection
Total cost: $35+ USD. You can get started creating a VPN server with a Raspberry Pi for as little as $35. If you opt for a Raspberry Pi Zero or Zero W, that cost lowers even more. I recommend a Raspberry Pi 4, although virtually any Pi board should work. If you don't have a RasPi or any accessories, you might consider a starter kit.
What is the Purpose of this Raspberry Pi VPN Server?
When you subscribe to a VPN service such as IPVanish, VPN Unlimited, or Private Internet Access, you're routing internet traffic through servers in different locations to then mask your IP address. This might be to give you more security or allow access to different services. Building a Raspberry Pi VPN server affords the same functionality, but in this case you're connecting to a server, your Pi, running on your home network. So any client devices, like a phone or PC, will route traffic through your Pi and thus appear as though they're on your home network. If you're traveling abroad, you can connect to the Netflix of your home country by relying on a Raspberry Pi-based VPN server. Or perhaps you need to access files on your home server when traveling. Simply VPN into your home network for access.
Benefits of a Raspberry Pi VPN server:
- Access to home network
- Home server access while away
- Circumvent geo-restrictions and connect to services like Netflix from your home network while abroad
Make a Raspberry Pi VPN Server Using PiVPN
Arguably the easiest methods for running a Raspberry Pi VPN server is with PiVPN, an OpenVPN configuration too. As a word of caution: running PiVPN runs a script downloaded from the internet, so you'll want to trust the source. While I haven't personally scoured their GitHub codebase, everything seems to check out and it works like a champ on my Raspberry Pi.
Begin by running an update:
sudo apt-get update && apt-get upgrade
Next up, run the PiVPN installation script:
curl -L https://install.pivpn.dev | bash
If you prefer the unstable test branch, enter:
curl -L https://test.pivpn.dev | TESTING= bash
And that's it! Sort of. The script launches a PiVPN automated installer. You'll receive a message informing you that "This installer will transform your Raspberry Pi into an openvpn server!" Click Ok and continue.
Next up, select a static IP address, then hit Ok. Choose either wlan0 or eth0 for wireless or ethernet respectively. Highlight the option you wish to choose, press spacebar to add an asterisk beside that choice, then hit Ok when you're ready.
Then, there's a message asking if you'd like to use your current newtork settings as a static address. You can review your IP address. If you're satisfied, press Yes and continue.
PiVPN now confirms your IP address settings. Wait a bit, and you should now see a screen asking you to pick a local user to hold your OpenVPN configuration. Click Ok. Then, you should be able to select a user. On my Raspberry Pi, I had one option: Pi. Press the spacebar to select it and an asterisk will appear next to Pi. After that, hit Ok.
You'll be prompted to enable unattended-upgrades. Select Ok and continue. Next up you can either enable unattended-upgrades or not. Choose either yes or no. Once you've proceeded, apt-get will check for upgraded packages, as well as check if OpenVPN is installed. If it's not installed, PiVPN proceeds to install it.
If PiVPN begins installing OpenVPN, you'll see a notification about selecting an OpenVPN port. By default, that's 1194 but you can change it. I left this unchanged. Press Ok.
Confirm your OpenVPN port and hit Yes. Select your preferred encryption strength: 2048-bit (recommended, 1024-bit (test level), or 4096-bit (paranoid level). I left this as the recommended 2048-bit level. When you're satisfied, hit Ok.
A screen lets you know that default values for fields used in a security certificate will be reviewed. Select Ok, and review the different fields including country, state, city, and more. You can change these, or leave them as-is. I left them unaltered and pressed Ok. Again, confirm that these fields are correct and pick Yes.
OpenVPN will now create your encryption keys, so click Ok. Wait for your encryption to generate keys. Depending on your level of encryption, this might take a bit of time. Go grab a cup of coffee or a pint, walk your dog, or fire up your favorite video game while you wait. Upon completion, OpenVPN prompts you if you've got a public DNS entry you'd like to use versus a public IP address. Select your preferred option, and continue.
Should you opt for a DNS entry, PiVPN asks you to give your public DNS name. Then, pick a DNS provider such as Google and OpenDNS. Enter that and press Ok. Alternatively, selecting IP address lets you enter your IP address.
Installation is complete, and you can run pivpn add which will create ovpn profiles. You'll be prompted to reboot your Raspberry Pi so select Yes.
After restarting, go ahead and update again:
sudo apt-get update && apt-get upgrade
Then, configure your VPN client:
pivpn add
You'll need to select a name for your client and specify a password that will be used for connecting to this VPN. After you set up your first OpenVPN client, there's an .ovpn file for the newly-created client, and you need this to log in on a client device.
Install OpenVPN on the Raspberry Pi - Raspberry Pi OpenVPN
Alternatively, you may prefer to simply install OpenVPN for the Raspberry Pi on a Linux distro such as Raspbian, Debian, Ubuntu, Linux Mint, or another OS.
Begin by performing an update:
sudo apt-get update && apt-get upgrade
Next, install OpenVPN:
sudo apt-get install openvpn unzip
Check that your time zone information is correctly configured:
sudo dpkg-reconfigure tzdata
Select any add-on services, choose your country, region, and protocol, either UDP or TCP.
Make sure you're running with root privileges:
sudo -i
And download the OpenVPN set up:
cd /tmp && wget https://files.ovpn.com/raspbian/ovpn-se-gothenburg.zip && unzip ovpn-se-gothenburg.zip && mkdir -p /etc/openvpn && mv config/* /etc/openvpn && chmod +x /etc/openvpn/update-resolv-conf && rm -rf config && rm -f ovpn-se-gothenburg.zip
Then, enter your login user name and password:
echo "USERNAME" >> /etc/openvpn/credentials
echo "PASSWORD" >> /etc/openvpn/credentials
Now, start OpenVPN with:
sudo openvpn --config /etc/openvpn/ovpn.conf --daemon
And check your connection using:
curl https://www.ovpn.com/v2/api/client/ptr | python -m json.tool
To check that OpenVPN is running on your Raspberry Pi, enter:
ps aux|grep openvpn
Now, OpenVPN should be properly installed on your Raspberry Pi.
OpenVPN Clients and More
In order to connect to your Raspberry Pi VPN server, you'll need to run client software. For macOS, Tunnleblick is a solid choice. On Windows, you can use OpenVPN. And for Android or iOS mobile devices, OpenVPN Connect is a great option. Once you've got a client installed, you need to copy the client configuration .ovpn file to your device. Then, you can connect to your Pi VPN server.
How to Install Wireguard on the Raspberry Pi
Another excellent VPN option for tunneling is WireGuard. It's fast and secure, plus has benefitted from superb support from the Linux community. Although WireGuard initially debuted for Linux, it's since been ported to macOS, Windows, iOS, Android, and BSD. Because it's newer than the likes of OpenVPN, WireGuard boasts better security. Setting it up is easy with its cross-platform compatibility, and there's SSH functionality for remote control and management. Installation is a bit easier than with OpenVPN.
What's neat about WireGuard is that beginning with Linux kernel 5.6, it's included in the Linux kernel. So you won't need to manually add the kernel module if you're running a Linux distro on kerne. 5.6 or later.
Begin installing WireGuard on the Raspberry Pi by running an update:
sudo apt-get update && apt-get upgrade
Additionally, you'll need to update your Linux kernel headers:
sudo apt-get install raspberrypi-kernel-headers
Now, add the WireGuard repository to your trusted sources list:
echo "deb http://deb.debian.org/debian/ unstable main" | sudo tee --append /etc/apt/sources.list.d/unstable.list
If you're running Raspbian Buster, that's it. But for Debian Stretch-based distributions such as Raspbain Stretch, you'll need to install the dirmngr network operations utility:
sudo apt-get install dirmngr
Then add the necessary keys:
wget -O - https://ftp-master.debian.org/keys/archive-key-$(lsb_release -sr).asc | sudo apt-key add -
And enter:
printf 'Package: *\nPin: release a=unstable\nPin-Priority: 150\n' | sudo tee --append /etc/apt/preferences.d/limit-unstable
Run another update:
sudo apt-get update
And install WireGuard:
sudo apt-get install wireguard
Great! WireGuard should now be installed on your system. You can check if your installation completed by running:
lsmod | grep wireguard
If there's an output, WireGuard is installed, but if the output is missing, it's not. Once you finish, go ahead and reboot your Raspberry Pi:
sudo reboot
Configuring WireGuard on the Raspberry Pi for a Pi VPN
After installing WireGuard, you'll need to perform a bit of basic set up. Start by generating a public and private key pair for the WireGuard server. You can accomplish this using the WireGuard user management script or manually.
Install the WireGuard user management script:
sudo apt-get install git qrencode
Then, run:
git clone https://github.com/adrianmihalko/wg_config.git
Afterward, generate your private and public server keys:
cd wg_configwg genkey | tee server_private.key | wg pubkey > server_public.key
cat server_private.key
cat server_public.key
Now, edit your WireGuard server information:
cp wg.def.sample wg.def
nano wg.def
_INTERFACE=wg0
_VPN_NET=[IP ADDRESS]
_SERVER_PORT=51820
_SERVER_LISTEN=your.publicdns.com:$_SERVER_PORT
_SERVER_PUBLIC_KEY=5lFoBBjeLcJWC9xqS/Kj9HVwd0tRUBX/EQWW2ZglbDs=
_SERVER_PRIVATE_KEY=aA+iKGr4y/j604LtNT+MQJ76Pvz5Q5E+qQBLW40wXnY=
And edit your client template as well:
nano client.conf.tpl
[Interface]
Address = $_VPN_IP
PrivateKey = $_PRIVATE_KEY
[Peer]
PublicKey = $_SERVER_PUBLIC_KEY
AllowedIPs = [YOUR IP ADDRESSES]
Endpoint = $_SERVER_LISTEN
You can pull up the WireGuard interface with:
sudo touch /etc/wireguard/wg0.conf
sudo wg-quick up wg0
[#] ip link add wg0 type wireguard
[#] wg setconf wg0 /dev/fd/63
[#] ip link set mtu 1420 up dev wg0
sudo wg
interface: wg0
listening port: 37165
Once that's finished, add your user:
sudo ./user.sh -a client1
Finally, restart WireGuard:
sudo wg-quick down wg0
You might wish to configure the wg0 interface to automatically start on first boot:
sudo systemctl enable wg-quick@wg0
Created symlink /etc/systemd/system/multi-user.target.wants/wg-quick@wg0.service → /lib/systemd/system/wg-quick@.service.
Install WireGuard VPN Clients
With WireGuard installed on your Raspberry Pi, you can connect to your home network. But you'll need to install a WireGuard client on your device such as an Android, iOS, or macOS device. When setting up a client, first download your preferred WireGuard client.
Then, add a new WireGuard tunnel. You have a few options:
- Create a from a file or archive
- Create from a QR code
- Create from scratch
Select the option you wish to use, then name your tunnel. Allow WireGuard to add VPN configurations on your device. Depending on what WireGuard client you're using, the configuration might vary a bit but it should generally be similar across all clients.
How to Install Surfshark on the Raspberry Pi
Surfshark is a popular VPN service you can run on the Raspberry Pi. Although it's a relative newcomer in the VPN space, Surfshark has achieved cult status because of its balance of speed and security. Installing Surfshark on the Raspberry Pi is pretty simple.
Head over to the Surfshark website and create an account for your Surfshark credentials.
After that, head under Devices > Manual.
Locate your service credentials at the bottom of the page. Use the username and password you created earlier to log into Surfshark from your Raspberry Pi.
For running Surfshark on the Raspberry Pi, you can use OpenVPN as a virtual private network server client. Begin by making sure your system is up to date:
sudo apt update
sudo apt upgrade
Now, install OpenVPN on the Pi:
sudo apt install openvpn unzip
Then, alter the OpenVPN directory and download configuration files:
cd /etc/openvpn
sudo wget https://account.surfshark.com/api/v1/server/configurations
And unzip the Surfshark config files:
sudo unzip configurations
Remove the config archives:
sudo rm configurations
Use the ls command to view all available config files for Surfshark VPN:
ls
Locate the OVPN file you want to connect to, and set Surfshark to connect to it:
sudo openvpn PREFERRED_OVPN_FILE
While establishing a server connection, you'll need to enter your Surfshark service credentials, the ones you set up earlier. Once that's complete, you should be able to connect to Surfshark.
How to Set Up a Port Forward
In order to access your Raspberry Pi VPN server from outside of your home network, you'll need to configure a port forward. Setting up a port forward varies a bit based on your router, but it's generally the same. Begin by accessing your router. It's probably at an address such as 192.168.0.1, 192.168.1.1, 192.168.2.1, or another common default address. On my Linksys router, it was 192.168.1.1.
Once you've accessed your router, you'll need to login. The default user name is admin and the password at default is usually admin. If you're like most users, you never bothered to change this, but if you did, congrats! Enter your custom user name and password.
Find a section that reads Port Forwarding, Apps and Gaming, or something similar. Each router is different. My Linksys showed this setting under Security > Apps and Gaming > Single Port Forwarding. There are options for Port Range Forwarding and Port Range Triggering as well.
Enter your information such as a port range or port number. For a single port, you'll enter the same number for Internal and External. Or, for a range, use Start and End. The website PortForward shows many frequently-used ports. Input information such as UDP, TCP, or all. And of course, type in your static IP where it's specified. Toggle your port forward to either on or enabled. Then, you should be good to go. Again, the login and wording varies somewhat by router manufacturer, but it's generally standard.
Run OpenVPN on your Raspberry Pi - Final Thoughts
An OpenVPN Raspberry Pi server works extremely well. Small, energy-efficient, and with a simple OpenVPN installation, the Pi is a fantastic always-on VPN server option.

















Leave your feedback...